Get 30% off ITprotv.com with PROMO CODE CCNADT
https://www.itpro.tv/
Follow me on Twitter:
https://twitter.com/CCNADailyTIPS
Previous Video:
Implement Static NAT on Cisco ASA Using the CLI:
https://youtu.be/OqBm-jTfUwE
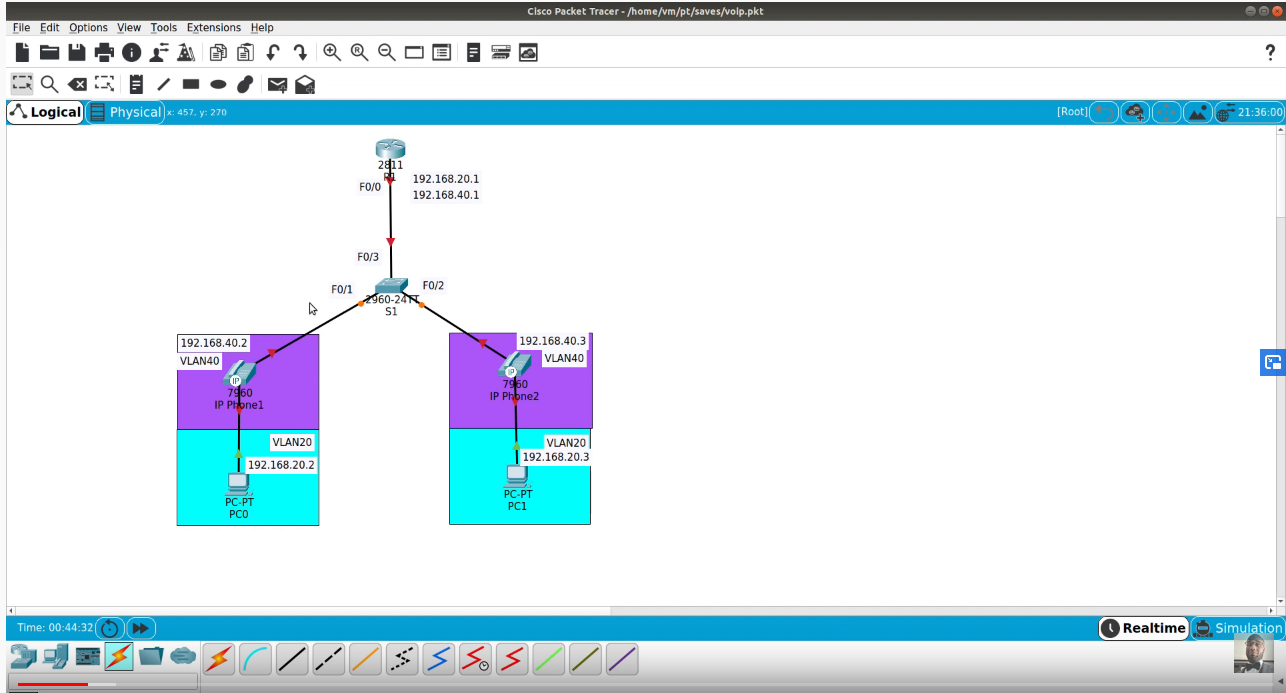
Dynamic NAT
Dynamic NAT assigns a random IP address from a preconfigured pool of global IP addresses. The security appliance uses a one-to-one methodology by allocating one global IP address to an inside IP address. Hence, if 100 hosts reside on the inside network, then you have at least 100 addresses in
the pool of addresses. After the security appliance has built a dynamic NAT entry for an inside host, any outside machine can connect to the assigned translated address, assuming that the security appliance allows the inbound connection.
Dynamic NAT
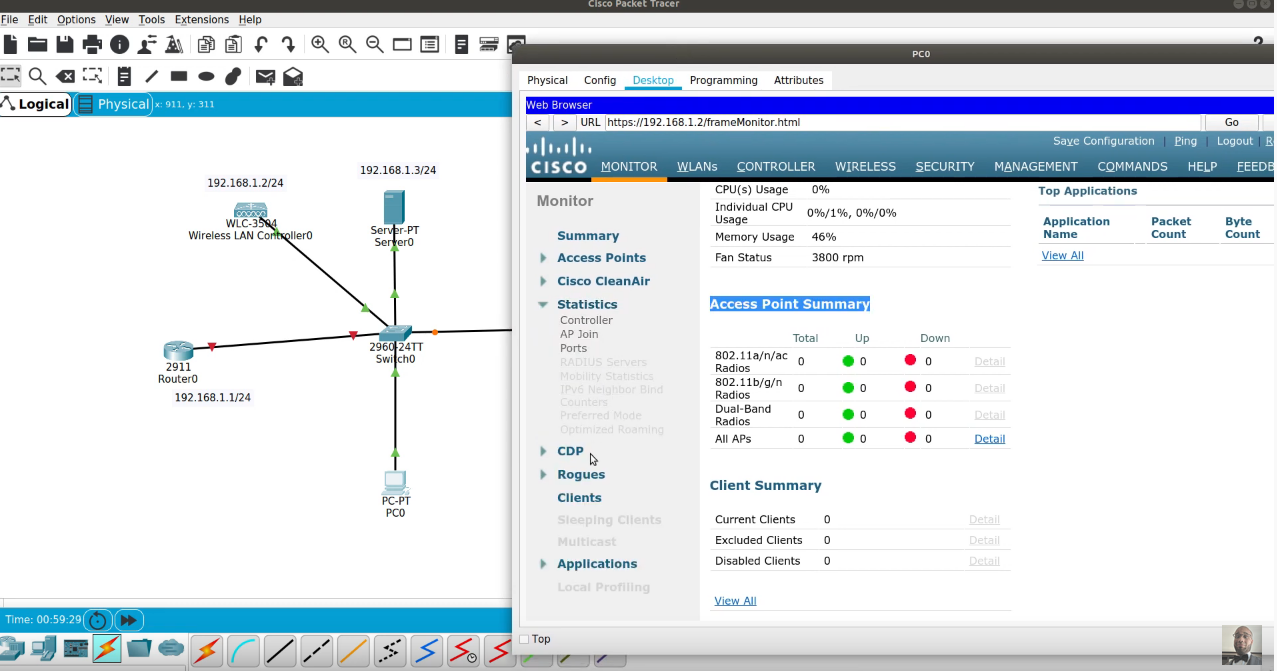
Usually you would configure translation using a subnet that does not physically exist. For simplicity of routing in our scenario, we will create a pool of addresses from the 209.165.201.0/27 subnet that is assigned to the outside interface on the ASA. Using ASDM, navigate to Configuration > Firewall > Objects > Network Objects/Groups. Select the inside-network object group and click Edit.
Dynamic NAT involves having a pool of global addresses and only mapping those global addresses to inside devices when those inside devices have and need to go out to the Internet.