Get 30% off ITprotv.com with PROMO CODE CCNADT
https://www.itpro.tv/
Follow me on Twitter:
https://twitter.com/CCNADailyTIPS
Previous Video:
https://youtu.be/M93wGykQpXo
VLAN hopping
In a basic VLAN hopping attack , the attacker takes advantage of the fact that Dynamic Trunking Protocol (DTP) is enabled by default on most switches. The network attacker configures a system to use DTP to negotiate a trunk link to the switch.
As a result, the attacker is a member of all the VLANs that are trunked on the switch and can “hop” between VLANs. In other words, the attacker can send and receive traffic on all those VLANs. The best way to prevent a basic VLAN hopping attack is to turn off DTP on all ports, and explicitly configure trunking mode or access mode as appropriate on each port.
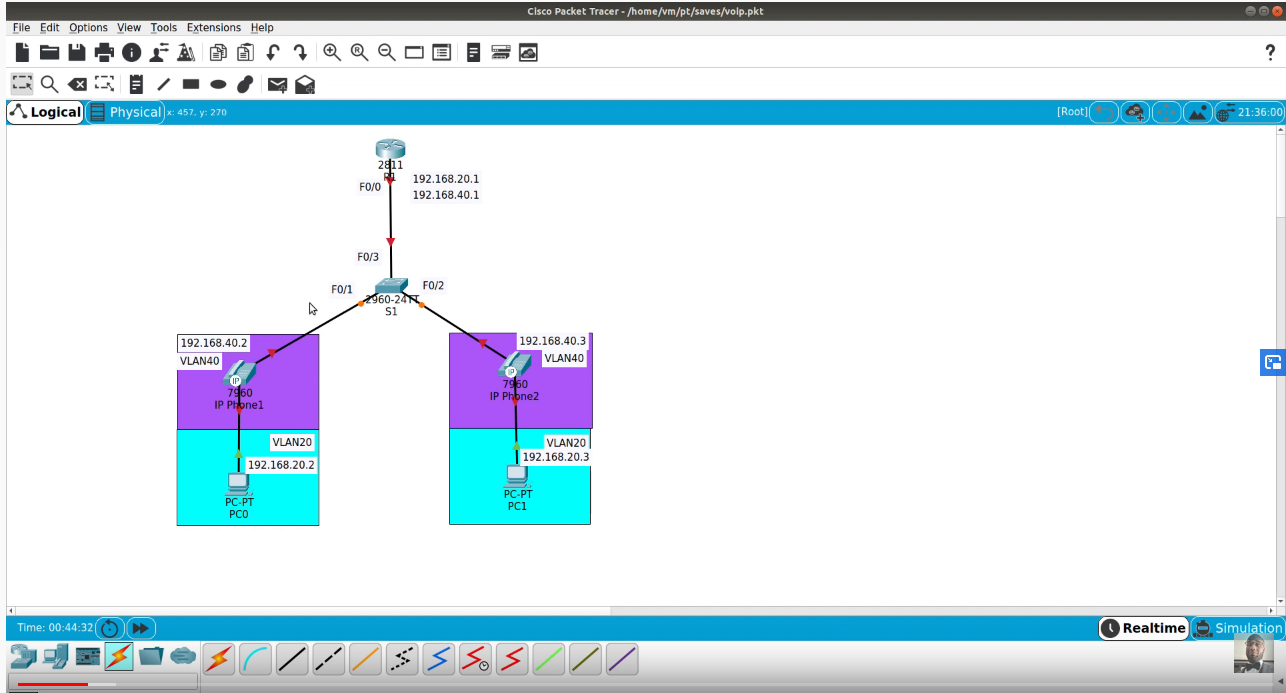
VLAN Double Tagging
The double-tagging (or double-encapsulated) VLAN hopping attack takes advantage of the way that hardware operates on some switches. Some switches perform only one level of 802.1Q decapsulation and allow an attacker, in specific situations, to embed a second 802.1Q tag inside the frame.
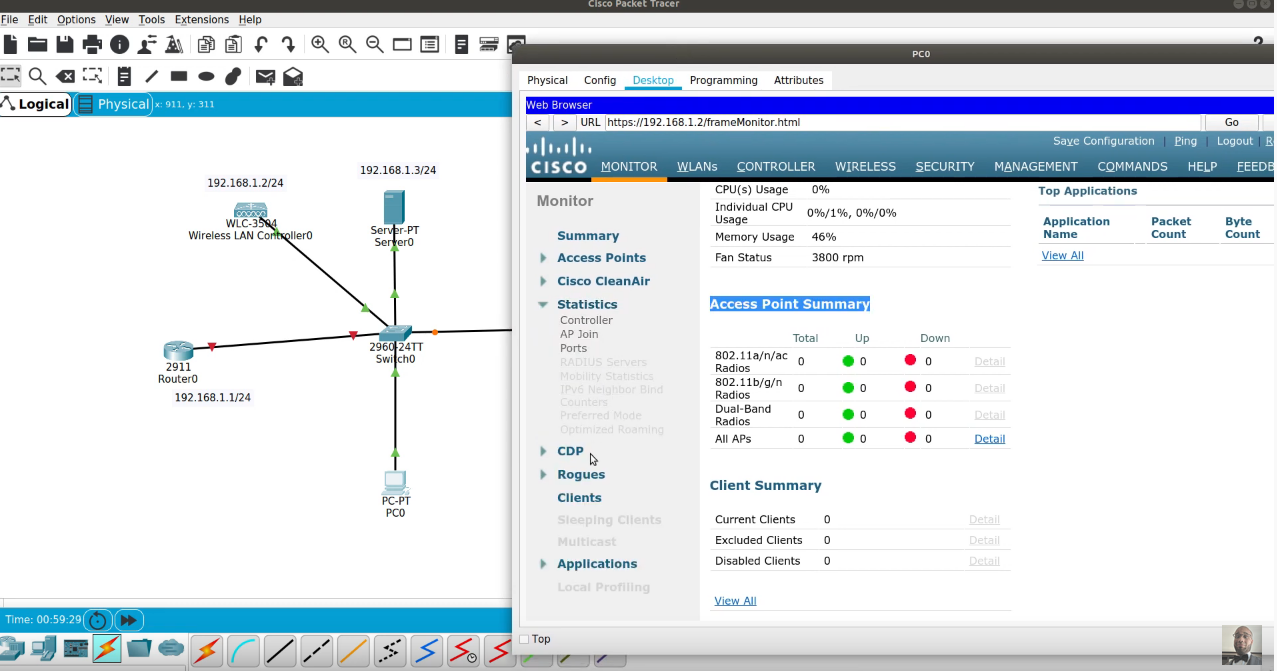
This tag allows the frame to go to a VLAN that the outer 802.1Q tag did not specify. An important characteristic of the double-encapsulated VLAN hopping attack is that it can work even if DTP is disabled on the attacker’s access port. Figure 14-4 illustrates an example of the VLAN hopping attack using double-tagging to allow access to the victim’s VLAN (VLAN 20).
STP Attacks
A network attacker can use STP to change the topology of a network so that the attacker’s host appears to be a root bridge with a higher priority. The attacker sends out bridge protocol data units (BPDUs) with a better bridge ID and thus becomes the root bridge. As a result, traffic between the two switches passes through the new root bridge, which is actually the attacker system.
Mitigate STP Attacks
To mitigate STP manipulation attacks, use the Cisco STP stability mechanisms to enhance the overall performance of the switches and to reduce the time that is lost during topology changes. These are recommended practices for using STP stability mechanisms:
■ PortFast: PortFast immediately brings an interface configured as an access or trunk port to the forwarding state from a blocking state, bypassing the listening and learning states. Apply to all end-user ports. PortFast should only be configured when there is a host attached to the port, and not another switch.
■ BPDU Guard: BPDU guard immediately error disables a port that receives a BPDU. Typically used on PortFast-enabled ports. Apply to all end-user ports.
■ Root Guard: Root guard prevents an inappropriate switch from becoming the root bridge. Root guard limits the switch ports out of which the root bridge may be negotiated. Apply to all ports that should not become root ports.
■ Loop Guard: Loop guard prevents alternate or root ports from becoming designated ports because of a failure that leads to a unidirectional link. Apply to all ports that are or can become non-designated.