Get 30% off ITprotv.com with PROMO CODE CCNADT
https://www.itpro.tv/
Follow me on Twitter:
https://twitter.com/CCNADailyTIPS
Previous Video:
https://youtu.be/YQyLhaH0yog
Kali Linux GNS3
https://www.gns3.com/marketplace/appliance/kali-linux-2
CAM OverFlow
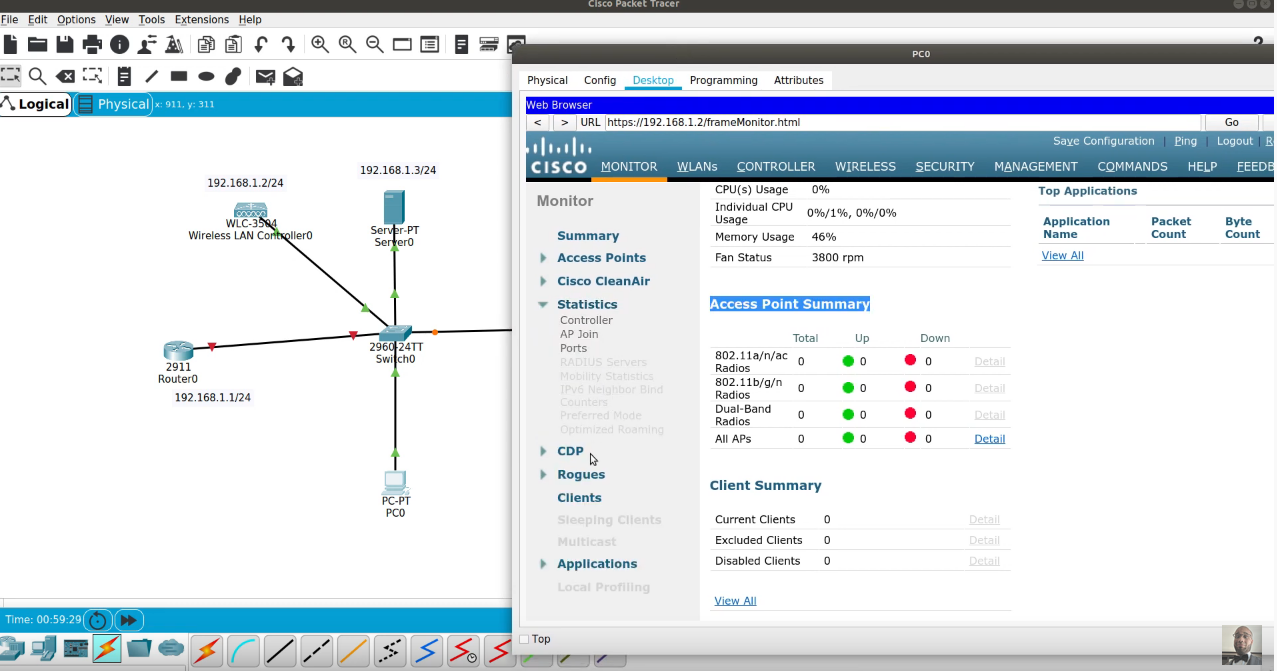
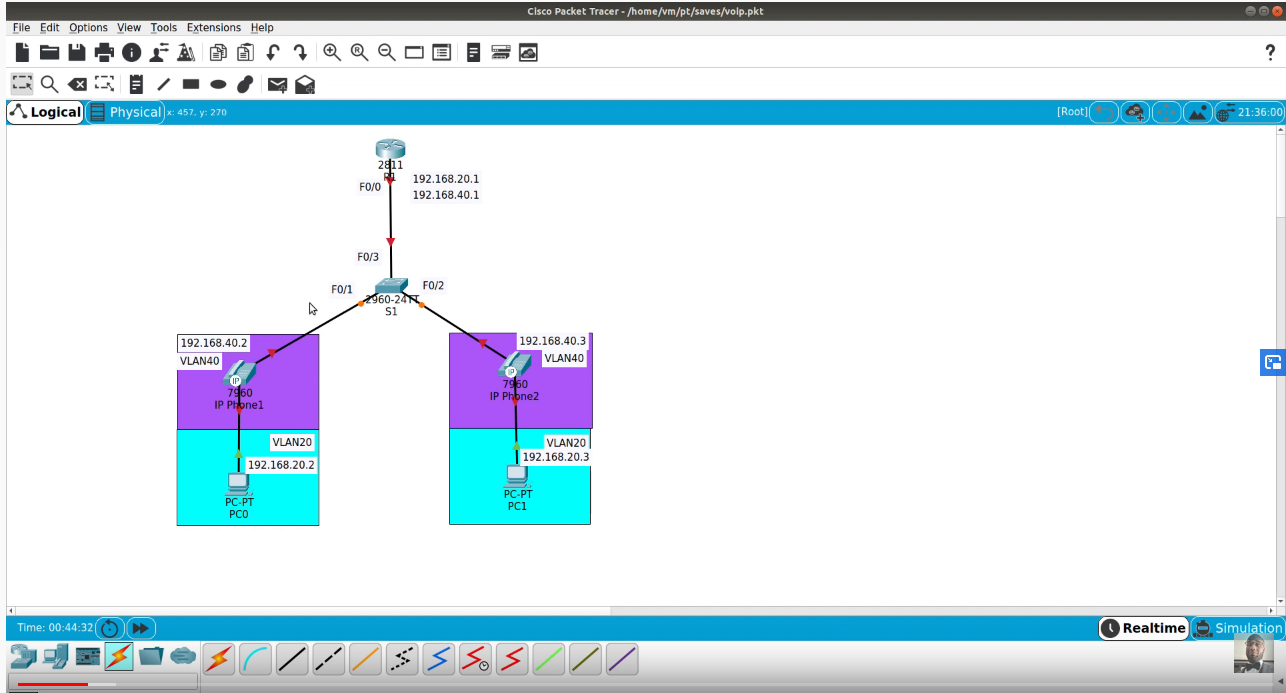
A CAM overflow attack occurs when an attacker connects to a single or multiple switch ports and then runs a tool that mimics the existence of thousands of random MAC addresses on those switch ports. The switch enters these into the CAM table, and eventually the CAM table fills to capacity. When a switch is in this state, no more new MAC addresses can be learned; therefore, the switch starts to flood any traffic from new hosts out of all ports on the switch.
A CAM overflow attack turns a switch into a hub, which enables the attacker to eavesdrop on a conversation and perform man-in-the-middle attacks.
Kali Linux
Kali Linux is a Debian-based Linux distribution aimed at advanced Penetration Testing and Security Auditing. Kali contains several hundred tools which are geared towards various information security tasks, such as Penetration Testing, Security research, Computer Forensics and Reverse Engineering. Kali Linux is developed, funded and maintained by Offensive Security, a leading information security training company.