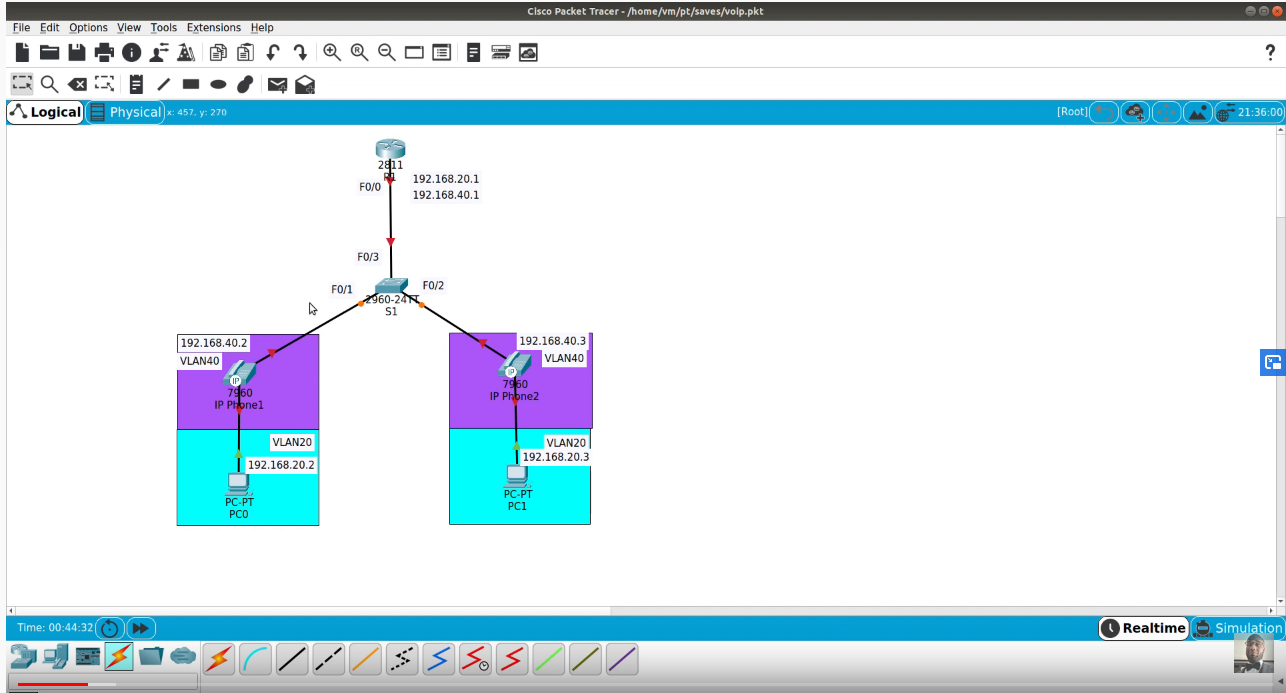
1.1 Configure, verify, and troubleshoot VLANs (normal/extended range) spanning multiple switches
1.1.a Access ports (data and voice)
1.1.b Default VLAN
1.2 Configure, verify, and troubleshoot interswitch connectivity
1.2.a Add and remove VLANs on a trunk
1.2.b DTP and VTP (v1&v2)
1.3 Configure, verify, and troubleshoot STP protocols
1.3.a STP mode (PVST+ and RPVST+)
1.3.b STP root bridge selection
1.4 Configure, verify, and troubleshoot STP-related optional features
1.4.a PortFast
1.4.b BPDU guard
1.5 Configure, verify, and troubleshoot (Layer 2/Layer 3) EtherChannel
1.5.a Static
1.5.b PAGP
1.5.c LACP
1.6 Describe the benefits of switch stacking and chassis aggregation
1.7 Describe common access layer threat mitigation techniques
1.7.a 802.1x
1.7.b DHCP snooping
1.7.c Nondefault native VLAN
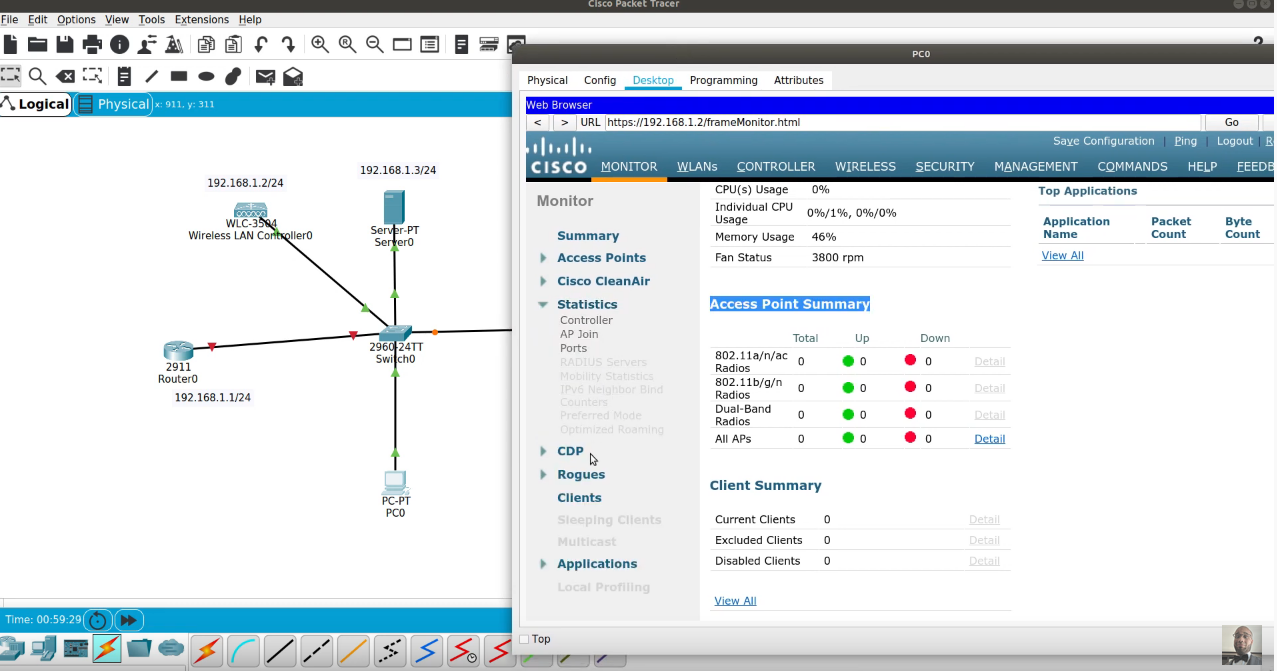
TACACS
TACACS+ is a security application that provides centralized validation of users attempting to gain access to a router or network access server. It services are maintained in a database on a TACACS+ daemon running, typically, on a UNIX or Windows NT workstation. You must have access to and must configure a TACACS+ server before the configured it features on your network access server are available.It provides for separate and modular authentication, authorization, and accounting facilities. TACACS+ allows for a single access control server (the TACACS+ daemon) to provide each service–authentication, authorization, and accounting–independently. Each service can be tied into its own database to take advantage of other services available on that server or on the network, depending on the capabilities of the daemon.
EtherChannel Overview
EtherChannel is a Cisco technology that enables the aggregation or bundling of switchports into one logical link. Bundling multiple switchport ethernet links into one logical channel increases bandwidth as well creating redundancy and fault tolerance. For example, a bundle of four switchports into one EtherChannel would provide four times the bandwidth coming to and from the switch. EtherChannel bundles or port groups can be run from switch-to-switch or switch-to-server if the server’s network interfaces cards (NICs) support EtherChannel. You can bundle up to eight switchports in one Etherchannel port group with no more than six EtherChannel port groups per switch.
Rapid PVST+
In this activity, you will configure VLANs and trunks, Rapid Spanning Tree PVST+, primary and secondary root bridges, and examine the configuration results. You will also optimize the network by configuring PortFast, and BPDU Guard on edge ports.
Configure Rapid Spanning Tree PVST+ Load Balancing
The Rapid Spanning Tree Protocol (RSTP; IEEE 802.1w) can be seen as an evolution of the 802.1D standard more so than a revolution. The 802.1D terminology remains primarily the same. Most parameters have been left unchanged so users familiar with 802.1D can rapidly configure the new protocol comfortably. In most cases, RSTP performs better than proprietary extensions of Cisco without any additional configuration. 802.1w can also revert back to 802.1D in order to interoperate with legacy bridges on a per-port basis.
Configure S1 to be the primary root for VLANs 1, 10, 30, 50, and 70. Configure S3 to be the primary root for VLANs 20, 40, 60, 80, and 99. Configure S2 to be the secondary root for all of the VLANs.
PortFast
PortFast causes a port to enter the forwarding state almost immediately by dramatically decreasing the time of the listening and learning states. PortFast minimizes the time it takes for the server or workstation to come online. Configure PortFast on S2 interfaces that are connected to PCs.
Understanding How PortFast BPDU Guard Works
To prevent loops from occurring in a network, the PortFast mode is supported only on nontrunking access ports because these ports typically do not transmit or receive BPDUs. The most secure implementation of PortFast is to enable it only on ports that connect end stations to switches. Because PortFast can be enabled on nontrunking ports connecting two switches, spanning tree loops can occur because BPDUs are still being transmitted and received on those ports.